Context
Post-merger, multiple identity providers and on-prem directories forced repeated logins, spreadsheet-driven role mapping, and weak answers to “why did this principal have this permission then?”. Leadership wanted convergence within a few quarters without freezing day-to-day operations, aligned to HR as the authoritative people source.
Constraints
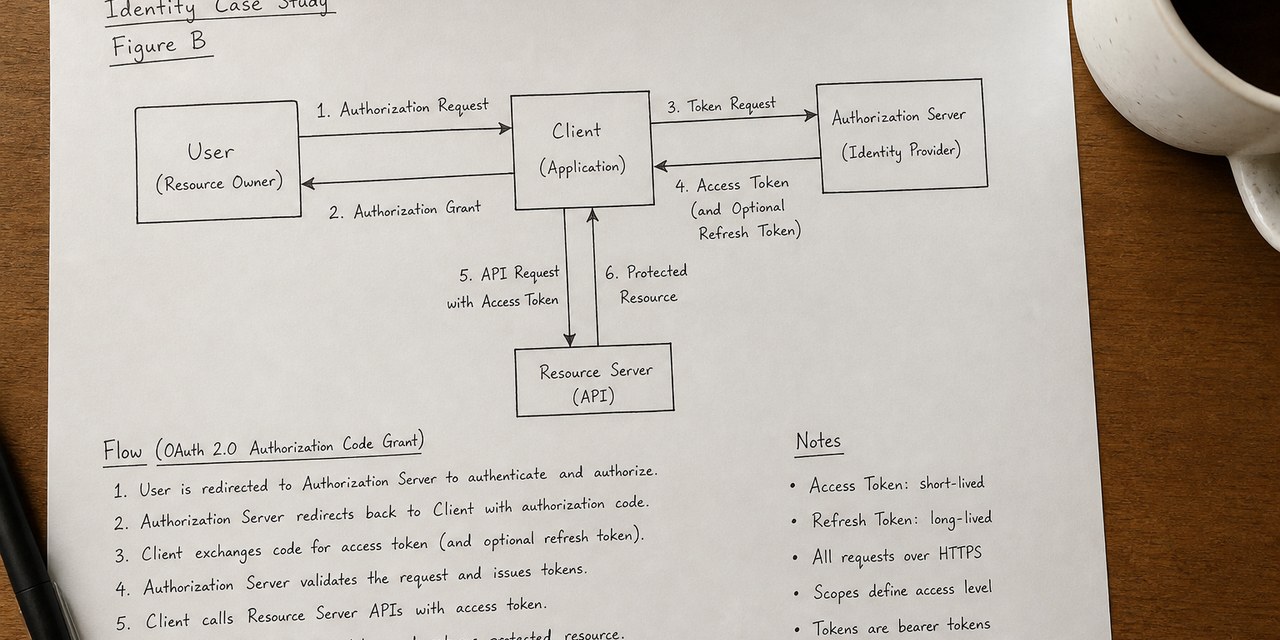
HR-driven attribute changes did not propagate uniformly, leaving stale roles. Token lifetimes differed across apps, creating subtle session-fixation exposure. Cross-region DNS and certificate misconfiguration intermittently broke mobile sign-in. Some legacy apps only accepted older SAML assertions while newer clients expected OIDC. Privileged access approvals still lived in email, disconnected from ticketing.
What we did
We introduced a single user-facing login path with consistent session timeouts, SCIM or reliable batch directory sync, and scheduled reconciliation jobs for orphan entitlements. Privileged roles gained stepped-up MFA and ticket-based approval. Dependent apps received standard OIDC metadata and health endpoints; CI validates TLS chains and JWKS rotation. Entitlement changes append to an auditable stream exportable by user or resource. A focused SAML adapter layer normalises legacy assertions and centralises login and attribute-change logging where short-term replacement was impossible.
Outcomes
Users see one login journey; temporary elevated access is ticket-bound and time-boxed. Audit sampling can reconstruct provenance in minutes. Mobile authentication failures dropped materially, and on-call guides were refreshed with escalation paths. The entry point can remain stable while underlying IdPs evolve in controlled phases.