Release incidents are expensive when teams cannot decide whether to roll back or cannot prove post-rollback consistency. The first deliverable is therefore not more buttons but runbooks with triggers, blast radius, and owners. Blue/green, canary, and feature flags are complementary: blue/green bounds infra cutover; canary bounds traffic share and metric gates; flags bound business-path kill switches.
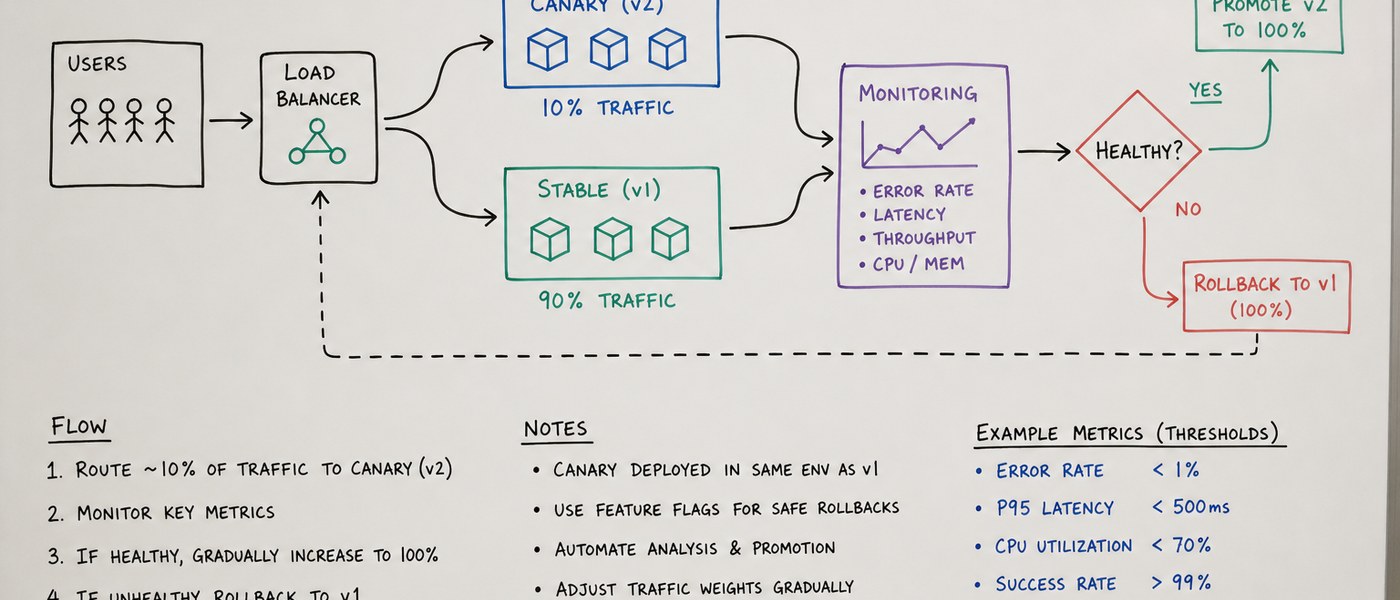
Canary releases must bind to SLOs and error budgets. CPU alone is a poor health signal; include error rates, latency percentiles, critical transaction success, and downstream saturation. Gate rules belong in pipeline configuration and are reviewed before go-live, not invented during an outage. When a gate fires a rollback, capture metric snapshots and build identifiers for post-incident review instead of debate-by-memory.
Database migrations and application releases should decouple. Expand/contract patterns or phased dual-write keep destructive changes split across cycles with a rollback path each time. Irreversible migrations should be explicitly marked “no automatic rollback” with business sign-off for downtime or read-only windows.
Feature flags need lifecycle metadata: creator, expiry, cleanup tasks, and audit fields. Long-lived flags become logic debt or “ghost configuration”. Sensitive regulatory paths should restrict who can change defaults and emit configuration audit events. Multi-environment releases need forward-compatible flag schemas to avoid production parse failures.
Release engineering cannot float free of process: without agreed change windows and freezes, advanced deploy tools get bypassed before holidays. Define “releasable” as a checklist—tests, performance baselines, validated rollback scripts, and escalation contacts. Tune all of this to your risk appetite.